During recent period of lockdown, the work of the association has not stopped and the activity has continued remotely from homes. This has brought yet again attention to security of the processing of personal data. Therefore, it is essential to revisit the subject of the GDPR implemented over two years ago. Let us go back to this law and its implications for charitable and cultural associations and foundations.
Despite the fact that GDPR is often known for the possibility of managing your preferences for processing your data, it goes much further. Due to the quantity and variety of data available to organisations, they have an important responsibility for the processing and maintaining the security of this data.
Who is affected by GDPR?
GDPR applies to the 27 countries of the EU to unify the rules and the legal framework for the processing of personal data and to allow the development of digital professional activities. This legal context is not set in stone since it adapts to follow developments in technologies and digital uses in our societies, thus building on the trust of users.
The General Data Protection Regulations concern any private or public company or organisation, regardless of its activity as long as it is established on the territory of the European Union or its activity targets European residents. Therefore, organisations established in countries other than those of the EU are also affected by these legal provisions. Even though the UK is leaving the EU, the UK will still need to comply with the GDPR. It will be incorporated into UK Data Protection law from the end of the transition period.
What is personal data?
Personal data is recognised by any information relating to an identified or trackable person, from single data to combination of several. It could be:
- direct data: surname, first name, photo, national insurance number, fingerprint
- indirect data: customer number, telephone number, address, date of birth
- sensitive data: Racial or ethnicity, religious belief, political opinion etc.
Within the framework of associations, foundations and NFPs, this data is numerous and essential if you want to be able to attribute a KPI score to your members, a perfect example in the context of data processing and cross-referencing.
But beware: personal data is not only found in your unused databases. Paper documents, even archives, can contain personal data: CV, register of members, register of volunteers, quotes and invoices from your service providers, tax receipts, beneficiary monitoring file etc. All of this data falls under the GDPR and should be treated the same as digital data.
What is data processing?
Processing data amounts to performing an operation or a set of operations on it, regardless of the processes used: collection of contact details via a questionnaire, update of supplier files, edition of a tax receipt, creation of a membership card etc.
The processing of personal data must be able to be justified: it must have an objective, be legal and be legitimate. In the context of the relationship with a member, this can translate into:
- soliciting the member for fundraising (objective)
- the member has given his consent to be solicited with “opt-in / opt-out *” (legal)
- the organisation wants to perform a (legitimate) action.
* opt-in / opt-out: agreement option / opt-out option
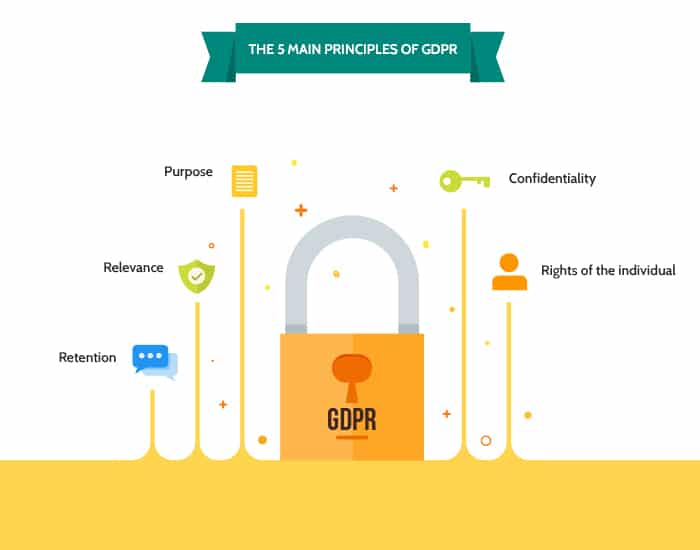
Purpose: the recording and use of data on an existing person must be done for a specific, legal and legitimate purpose.
Proportionality and relevance: the data collected must be limited to their relevance with regard to the purpose of the file.
Retention period: a retention limit must be set, depending on the type of data and the purpose of the file.
Confidentiality: data must be secure and only accessible and used by authorised persons.
Right of individuals: the owners of data have a right to access, rectify and consent to the use of these.
These principles can provide more information about IT structure within your organisation. It will show the ethics of data processing and reassure your members and other contacts about the security of it (especially if they provide you with their bank details).
Focus “safety”: what measures to take?
There are many risks associated with processing and handling data. Here are 10 things your organisation can do to protect itself and keep it safe.
-
- With an IT agreement, you make your contacts (members, benefactors, partners, service providers) aware that the data they send you may be subject to specific processing.
- Thanks to a password strategy, if you have a site allowing connection to a members area, offer your users (permanent staff, members, volunteers) the possibility of being able to identify themselves in complete security and schedule the password change regularly.
- Hard drive encryption is a great way to secure your staff’s workstations. Even not-for-profit organisations are not immune to loss or theft of a computer, especially laptops.
- If you are working remotely VPN access is the best solution to protect your organisation’s internal network. This also helps to avoid having to process data locally and reinforces the security of the previous point.
- You can also secure your server with access restrictions and only allow authorised people to access your servers.
- Continuing on from the previous point, managing the authorisations of your permanent staff allows you to ensure the confidentiality of information and only allow the persons concerned to modify and process personal data.
- It may seem like a no-brainer, but creating multiple backups helps ensure continuity of service in the event of a technical problem.
- Beyond protecting digital infrastructure and IT equipment, protecting premises with badge access can limit the risk of theft if you work in a building that hosts other associations or structures and where you have a lot of frequent visitors.
- Because you are in a field where collaboration is an absolute key to success, being able to secure your exchanges is essential. For this, FTPS / SFTP transfer is recommended to encrypt your communications and the transfer of your sensitive files.
Finally, you can also secure your websites with SSL access. This acronym, which may seem incomprehensible, corresponds to a specific protocol creating a secure channel between two machines communicating on the Internet or via an internal network.

